Modern vehicles evolve into centralized computing platforms, creating new cybersecurity challenges as critical and non-critical functions share hardware in software-defined vehicles.
Drivetech Partners
Modern vehicles are rapidly evolving from distributed electronics into centralized computing powerhouses that run both critical and non-critical functions on shared hardware. This shift to high-performance computing platforms within software-defined vehicles introduces significant cybersecurity challenges as the digital brain controlling everything from entertainment to braking must be protected against increasingly sophisticated threats.
Key Takeaways
- Centralized computing architectures are replacing distributed ECUs in modern vehicles, consolidating up to 150 separate units into fewer powerful computers
- The coexistence of safety-critical and non-critical software (mixed-criticality systems) on shared hardware introduces new security vulnerabilities
- Hypervisors and virtualization layers meant to isolate different functions are themselves vulnerable to misconfiguration and exploitation
- Expanded connectivity through OTA updates and third-party integrations has significantly increased attack surfaces
- Regulatory frameworks like ISO 26262 and ISO/SAE 21434 are evolving to address these new cybersecurity challenges

The Evolving Architecture of Software-Defined Vehicles
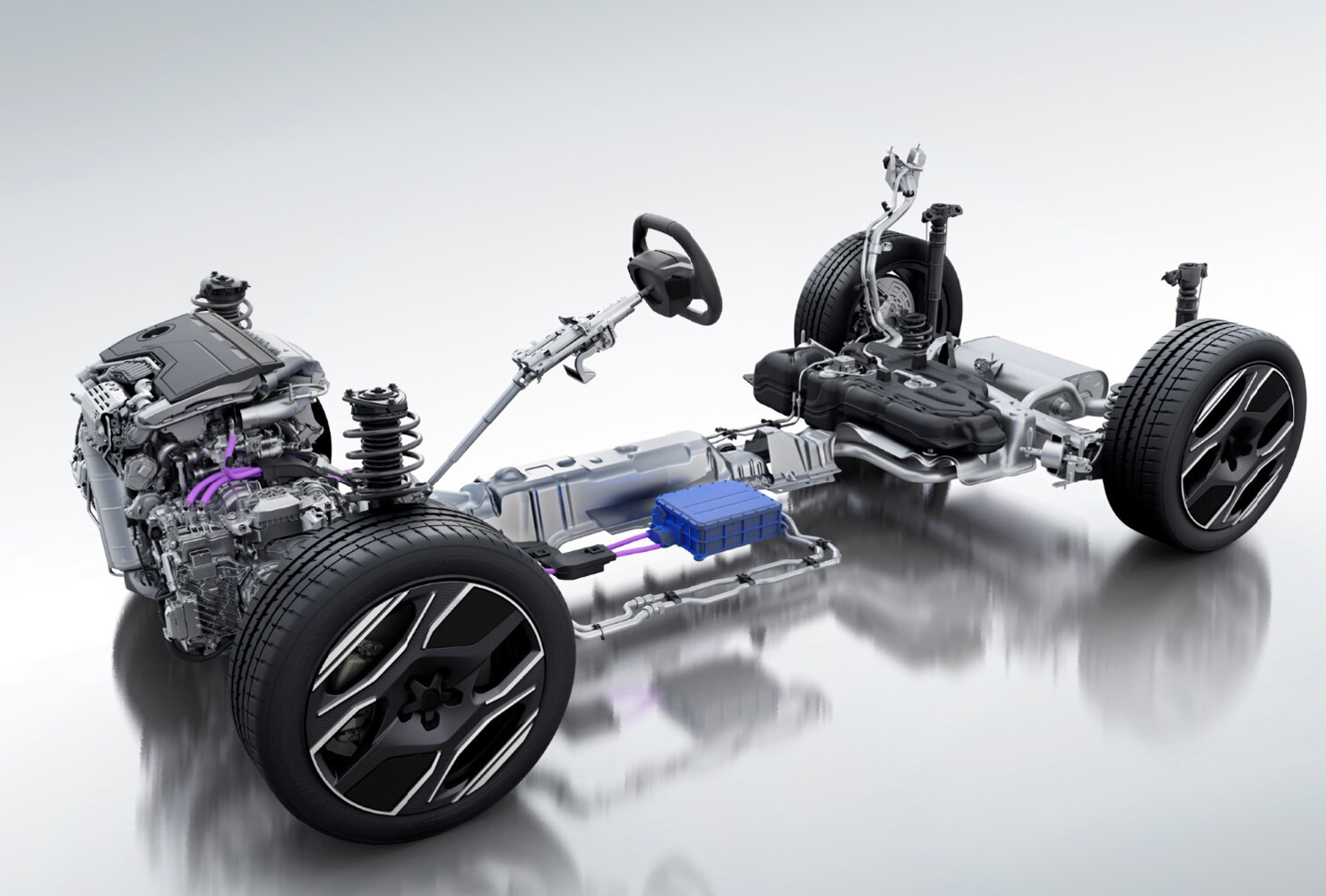
The automotive industry is undergoing a fundamental transformation in how vehicles are designed and built. Traditional architectures featuring 100-150 distributed electronic control units (ECUs) are giving way to centralized High-Performance Computing (HPC) platforms that consolidate numerous functions into fewer, more powerful computers.
This architectural shift delivers substantial benefits, including improved compute performance, increased standardization, and the ability to perform over-the-air (OTA) updates. However, it also introduces new security challenges. Increased connectivity through cloud connections, wireless updates, and third-party application integration has dramatically expanded the potential attack surface.
Modern software-defined vehicles now resemble computers on wheels rather than mechanical devices with electronic components. This shift creates opportunities for innovation but also makes vehicles targets for cyber threats previously limited to IT environments.
Mixed-Criticality Systems and Their Vulnerabilities
One of the most significant security challenges in modern vehicle design is the implementation of mixed-criticality systems. These systems run software with different safety importance levels on the same hardware platform. For example, your vehicle's infotainment system and braking control might share computing resources despite having vastly different safety implications.
The automotive industry uses ISO 26262 and the Automotive Safety Integrity Level (ASIL) framework to define risk levels from A (lowest) to D (highest). While this integration improves efficiency and enables new features, it creates risks of cross-domain compromises where non-critical systems might affect safety-critical functions.

To address these concerns, manufacturers implement hypervisors and virtualization layers to isolate different functions. However, these isolation mechanisms are themselves complex software that can be misconfigured or exploited. A vulnerability in the hypervisor could potentially allow an attacker to jump from a compromised infotainment system to safety-critical driving controls.
Expanded Attack Surface and Real-World Threat Landscape
The automotive threat landscape has expanded dramatically with the advent of connected vehicles. Legacy networking protocols like CAN and LIN were never designed for internet connectivity and become vulnerable when interfaced with modern systems.
Real-world incidents highlight these risks. In 2022, a security researcher discovered a method to hack Tesla vehicles remotely through third-party software, gaining partial control of vehicle functions. This incident demonstrated how interconnected features can create unexpected attack pathways.
The most common attack vectors in modern vehicles include:
- API vulnerabilities in connected services
- Supply chain exploits targeting third-party components
- Misconfiguration of cloud-connected ECUs
- Exploitation of over-the-air update mechanisms
These vulnerabilities are increasingly exploited for ransomware attacks, feature fraud (unlocking premium features without payment), and even vehicle theft. What makes automotive cybersecurity particularly challenging is that real-time constraints for safety-critical systems limit the types of security measures that can be implemented without affecting performance.
Supply Chain and Third-Party Software Risks
Modern vehicles incorporate software from dozens of suppliers, creating complex supply chain dependencies that are difficult to secure. Unmanaged third-party code and open-source components may introduce hidden vulnerabilities that vehicle manufacturers might not even know exist in their products.
Software Bills of Materials (SBOMs) are becoming crucial for visibility into components and dependencies. These detailed inventories help manufacturers track what code is in their vehicles and quickly respond when vulnerabilities are discovered in specific components.
Despite rigorous vetting processes, supply chain attacks represent a growing threat vector for sophisticated adversaries. A single compromised component from a trusted supplier can potentially affect thousands of vehicles, making supply chain security a critical focus area for the automotive industry.
Regulatory Framework and Compliance Challenges
The automotive industry faces an evolving regulatory landscape as governments and standards bodies work to address cybersecurity concerns. Key standards include:
- ISO/SAE 21434 - Automotive cybersecurity standard
- ISO 26262 - Functional safety for road vehicles
- UNECE WP.29 - Vehicle cybersecurity regulations
Compliance requirements are evolving rapidly as regulators catch up with technological advancement. Manufacturers must balance innovation speed with regulatory requirements across global markets, which often have different and sometimes conflicting standards.
Consistent enforcement across vendors and product lines remains challenging, and documentation and traceability requirements add complexity to development cycles. For many automotive companies, regulatory compliance has become a significant overhead cost in vehicle development.
Securing Virtualization and Ensuring Robust Isolation
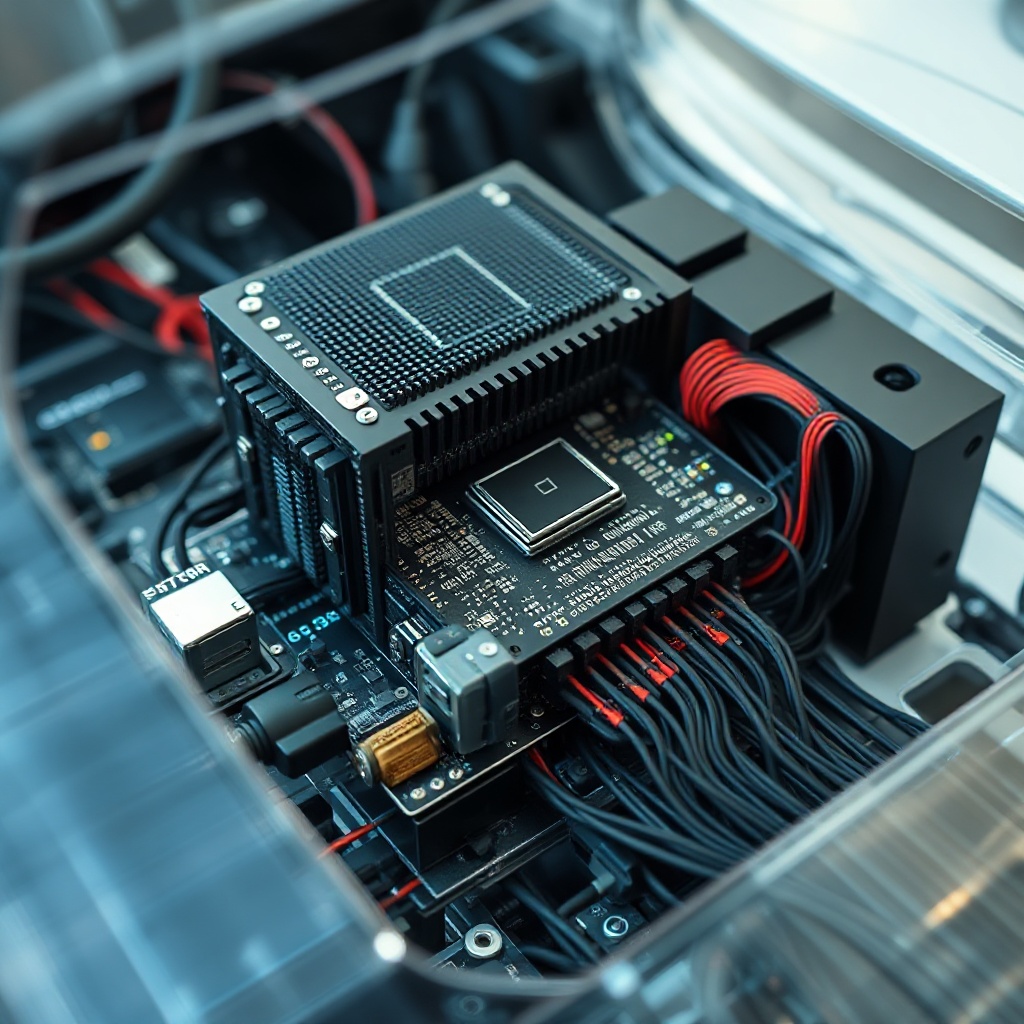
Hardware-enforced isolation is critical to prevent attacks from propagating between functional domains in mixed-criticality systems. Hypervisor hardening techniques must address both known vulnerabilities and zero-day exploits to maintain this isolation.
Regular testing for cross-domain vulnerabilities through specialized penetration testing is essential for validating security controls. These tests should specifically target potential pathways between non-critical and safety-critical systems.
Fail-safe mechanisms must guarantee that safety-critical functions retain execution priority during system degradation. Even under active cyberattack, vehicles must maintain real-time responsiveness for functions like steering and braking to ensure passenger safety.
Continuous Monitoring and Incident Response Strategies
As vehicles become more connected, continuous security monitoring becomes essential. Behavioral intrusion detection and prevention systems at both network and endpoint levels can detect threats in real-time before they cause harm.
Vehicle-specific security operations centers (SOCs) are emerging to monitor fleet-wide threats and coordinate responses across thousands of vehicles simultaneously. These operations centers use telemetry data from connected vehicles to identify patterns that might indicate coordinated attacks.
Automated rollback measures are crucial to prevent compromise during OTA updates. If an update contains malicious code or introduces vulnerabilities, the vehicle must be able to revert to a previous safe state automatically.
Secure boot, code signing, and end-to-end encryption serve as foundational security elements for all vehicle systems. Incident response plans must account for mobile assets with intermittent connectivity, as vehicles may not always be connected to networks that can deliver security patches.
Emerging Technologies and Future Security Directions
The integration of machine learning and AI in vehicles creates both opportunities and risks for cybersecurity. These technologies can help detect anomalies and potential attacks, but they also introduce new attack surfaces and potential vulnerabilities if the AI models themselves are compromised.
Hardware security modules, encrypted communication protocols, strong authentication mechanisms, and in-car firewalls are becoming critical technologies for automotive cybersecurity. These technologies form the foundation of a defense-in-depth strategy for protecting vehicle systems.
Mixed-criticality systems are becoming the default automotive design pattern for balancing innovation, safety, and cybersecurity. Continuous risk assessment methodologies are evolving to address the dynamic nature of software-defined vehicles and their constantly changing threat landscape.
Zero-trust architecture principles, traditionally used in enterprise IT environments, are being adapted for automotive environments. In this model, no component or system is trusted by default, regardless of its location within the vehicle network, requiring continuous verification for all access requests.
Sources
Arm Newsroom - Cybersecurity: The Enabler of Software-defined Vehicles
Automotive IQ - Cybersecurity Challenges in the Era of Software-Defined Vehicles
T-Systems - Automotive security for software-defined vehicles
BlackBerry Blog - Why Mixed-Criticality Is the Future of Automotive Architectures
AutoSens - The Evolving Architectures of Software-Defined Vehicles
Wipro - Implement Mixed Criticality Systems for Automotive Safety