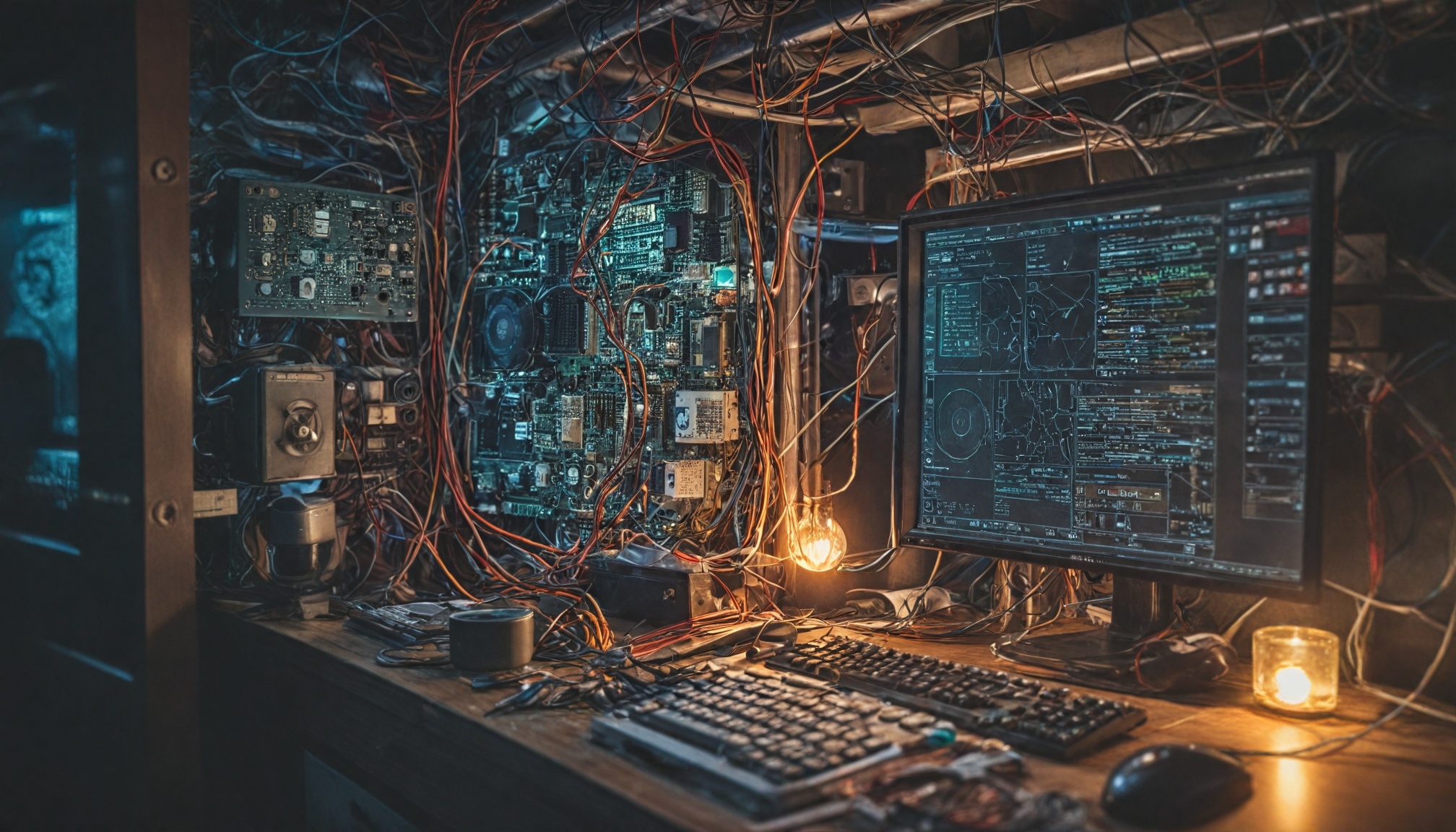
Debunking dangerous cybersecurity myths that leave you vulnerable. Learn why single solutions fail, everyone is a target, and your personal data is more valuable than you think.
Drivetech Partners
The pervasive misconceptions about cybersecurity create a dangerous false sense of security for both individuals and organizations, leading to exploitable vulnerabilities and preventable breaches. Many people place blind faith in single-solution tools like antivirus software or VPNs, grossly underestimate the value of their personal data, and mistakenly believe they're too small to be targeted by hackers.
Key Takeaways
- No single security solution offers complete protection - effective security requires multiple layered defenses working together
- Your personal information can be worth over $1,000 on the dark web, making everyone a valuable target regardless of wealth or status
- Security indicators like HTTPS padlocks and password-protected Wi-Fi create false confidence while leaving critical vulnerabilities unaddressed
- Small businesses and individuals make up prime targets for hackers due to typically weaker security measures and less awareness
- Human error remains the primary entry point for successful cyberattacks, highlighting the need for comprehensive security awareness

The Deadly Myth of Single-Solution Security
Many users falsely believe that installing antivirus software or a VPN alone provides complete protection against cyber threats. This dangerous misconception leaves their digital lives exposed. The reality is far more complex - over 70% of modern attacks start from malicious websites that antivirus alone can't always detect or block.
While antivirus programs can catch known malware, they struggle with zero-day vulnerabilities and sophisticated social engineering attacks. Similarly, VPNs provide excellent encryption for your connection but do nothing to prevent you from clicking on phishing links or downloading infected files.
Effective security requires a layered approach combining multiple tools:
- Comprehensive antivirus protection
- Secure VPN connections
- Properly configured firewalls
- Regular software updates
- User education and vigilance
Your Personal Data Is a Gold Mine for Criminals
One of the most dangerous myths is the belief that your personal information has little value to criminals. This couldn't be further from the truth. Individual personal information packages can fetch over $1,000 on dark web marketplaces, where criminals purchase credentials for banking, social media, and even materials to create forged documents.
Those "unimportant" personal accounts you rarely use? They're valuable assets for identity theft, credential stuffing, and sophisticated social engineering attacks. Criminals use seemingly minor details about your life to build convincing impersonation attempts or gain access to more valuable accounts.
The myth that personal data lacks value leads to careless protection habits. When you understand that every piece of personal information has value in the criminal ecosystem, you're more likely to take appropriate security measures across all your accounts.
Security Indicators That Create False Confidence
I often see users placing excessive trust in superficial security indicators that provide a false sense of safety. The HTTPS padlock icon only encrypts the connection between your device and the website - it says nothing about whether the site itself is legitimate or secure. Many phishing sites now use valid SSL certificates to appear trustworthy.
Similarly, password-protected Wi-Fi networks create an illusion of security. These can be compromised through weak passwords, rogue access points, or man-in-the-middle attacks. Public Wi-Fi remains dangerous even with passwords unless you use additional protection like a properly configured VPN.
Even strong passwords have limitations. While they're essential, they can still be bypassed through phishing, keyloggers, and social engineering tactics. Don't let these security indicators lull you into a false sense of safety when much more protection is needed.

Size Doesn't Matter: Why Small Targets Are Prime Targets
The myth that hackers only target large organizations is dangerously misleading. Small businesses and individuals actually comprise a significant portion of cyberattack victims due to their typically weaker defenses. According to the UK Cyber Security Breaches Survey, 32% of UK companies and 24% of charities reported breaches in the past year.
Cybercriminals operate with business-like efficiency, seeking maximum returns with minimal effort. They often prefer numerous easy targets over high-profile organizations with stronger security measures. Small entities frequently lack resources for comprehensive security, making them attractive "low-hanging fruit" for automated attacks and credential stuffing operations.
If you run a small business or manage your personal digital life with the assumption that you're "too small to target," you've already made yourself vulnerable. Hackers don't discriminate by size - they look for the path of least resistance to valuable data.
Beyond Technology: The Human Element in Security
Despite advanced security technologies, human error remains the primary cause of successful cyberattacks. Only 38% of UK companies feel highly confident managing cyber risks despite significant technology investments, highlighting the critical gap between technical solutions and human behavior.
The statistics are sobering: 43% of employees with sensitive work information on personal devices have been targeted by phishing. Today's sophisticated phishing attempts no longer contain obvious red flags like misspellings or poor grammar - they're professionally crafted to deceive even security-conscious users.
Cybersecurity cannot be relegated to IT departments alone. It requires collective responsibility, with every individual playing an active role in maintaining security. This means questioning unusual requests, verifying identities through secondary channels, and maintaining healthy skepticism when handling sensitive information or credentials.
How These Myths Create Attack Opportunities
Complacency and false confidence in outdated security practices create significant security gaps that attackers actively exploit. Modern cybercriminals don't rely on chance - they systematically target these predictable security blind spots using automation, social engineering, and emerging attack vectors.
Data breaches cascade across platforms through credential reuse. When credentials from one site are compromised, attackers immediately try those same username/password combinations on high-value services like banking, email, and cloud storage. This interconnected vulnerability means a single breach can threaten your entire digital identity.
Perhaps most concerning, successful attacks often remain undetected until substantial damage occurs. By believing common security myths, users create predictable security behaviors that hackers have learned to exploit with frightening efficiency.
Building Genuine Digital Resilience
True security requires implementing defense-in-depth strategies with multiple security layers working together cohesively. This approach acknowledges that no single solution is flawless, so redundant protections are essential.
Start by conducting regular risk assessments and patching vulnerabilities promptly. Use password managers like LastPass or KeePass to create and store unique, complex credentials for each account - this simple step addresses the critical weakness of password reuse.
Enable multi-factor authentication (MFA) on all important accounts, adding a crucial second layer of verification beyond passwords. Stay informed about emerging threats and adjust your defenses accordingly, treating security as an ongoing process rather than a one-time setup.
Test your incident response plans with simulated attacks to identify weaknesses before real attackers do. This proactive approach builds real resilience rather than false confidence in outdated security measures.
Creating a Culture of Security Awareness
For organizations, effective security requires cultivating a strong culture of security awareness. Mandate cybersecurity training for all staff, contractors, and vendors who access your systems, focusing on practical threat recognition and response procedures.
Incorporate security awareness into daily routines and organizational values, making secure practices part of your identity rather than burdensome requirements. Develop clear policies for reporting suspicious activity and potential breaches, emphasizing that early reporting is valued even if the threat turns out to be benign.
Recognize and reward security-conscious behaviors to reinforce positive habits. Finally, engage professional security assessments to identify and address blind spots in your defenses - external experts often spot vulnerabilities that insiders miss due to familiarity or assumptions.
By addressing these common cybersecurity myths with practical, layered defenses and ongoing vigilance, you can build genuine digital resilience against constantly evolving threats.
Sources
Eckoh - 10 Common Cyber Security Myths
StaySafeOnline - 6 Cybersecurity Myths Debunked
Insurance Business Magazine - How Much Is Personal Data Worth on the Dark Web
AZTech IT - Cybersecurity Myths & Misconceptions